EB has successfully executed mass-production-approved security components on the application layer for multiple functions and use cases. Our customers include car manufacturers like Audi, BMW, Daimler, Volkswagen, GM, and various Tier 1 suppliers.
Because of our many years in the field, we are able to offer:
EB zentur Key Management
Centralized key handling eases the use of keys and simplifies the complexity of application architectures. EB zentur Key Management designs and implements appropriate methods to handle cryptographic keys on various levels: from ECUs to overall key management solutions for OEMs and Tier 1s.
Features:
- Key generation and key distribution
- Symmetric and asymmetric key handling
- Storage and update of keys in ECUs
- Key request management from different software features
EB zentur Function Enabling
Enable new business models through secured activation of additional or updated features. Reduce costs for hardware variants by distinguishing feature sets in software through a secure manner.
Features:
- Manage license keys in the car
- Activate or deny features in the car
- Coupling of licenses to specific identities e.g. of a vehicle or a person
EB zentur Anti-Theft
EB’s anti-theft mechanism prevents re-use of stolen ECUs in new environments like non-authorized vehicles. This makes stealing ECUs unattractive and lowers insurance rates for car models that contain EB software.
Features:
- Prevent usage of ECUs in non-authorized vehicles, by coupling ECUs to the respective vehicle
- Long-term support during the entire lifecycle of a vehicle, from production to the vehicle in service and end-of-life scenarios
EB zentur Mileage Protection
Be prepared for legal requirements with EB’s mileage tampering protection mechanism. It detects as well as protects against manipulation and fraud attempts of original mileage values of vehicles.
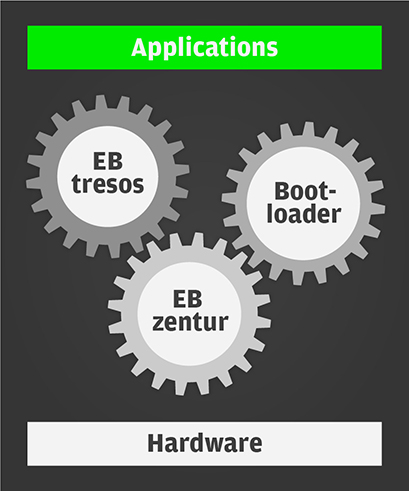
EB’s embedded security products
Software for hardware security modules
The security AUTOSAR basic software stack



